I've been studying the security aspects of network protocols and decided to take a look on the protocol used by a fun online game called "Among Us". If you don't know it, the game is very similar to the old board game "Clue". Do you remember "The assassin was colonel Mustard, with the candlestick, in the library"?
In Among Us you play as a member of a spaceship crew. At the beginning of the game, one of the players is randomly selected to play as an "impostor". The objective of the impostor is to kill everyone else, and the objective of the other players is the identify the impostor before it kill everyone.
I was trying to figure out if someone could cheat the game by looking in the data transmitted by the game server, in order to identify the impostor BEFORE the game starts.
So, I started analyzing the network protocol used by the game, and figured out all the data is being transmitted without no encryption. Ok, this is a simple game, made by brave indie developers, so no complex cryptography would be expected, anyway.
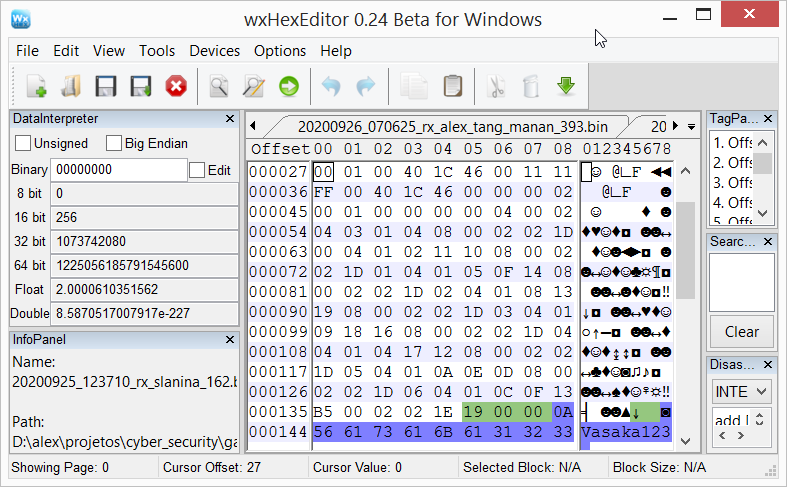
Of course, that doesn't mean it's totally easy to cheat by just reading the data. The game protocol is proprietary, and it is used to transmit a lot of data. Great effort would be necessary to decode the full protocol and be able to read things like players positions and other useful information.
However, I just needed to figure out if the impostor name is actually transmitted to all other players before the game starts. I didn't wanted to fully understand their protocol. So, in just a few hours of work, I came across to the exact datagram where this information is transmitted to all clients. So, a simple Python script was able to search for this information in real-time, during the game.
You can check the results in the following video:
Important: This cheat is just a proof of concept that I did only for research reasons! I'm not releasing this code (Please, do not ask for it). Among Us is a nice game and everyone should keep enjoying it without cheaters spoiling the fun! I hope the developers have some time to fix this vulnerability soon.